Not every decentralized wallet works the same way. Some are designed for fast Web3 access, while others are built for long-term storage. The “best” option usually depends on how often you transact and how much responsibility you want to take on for backups and security.
Hot Wallets
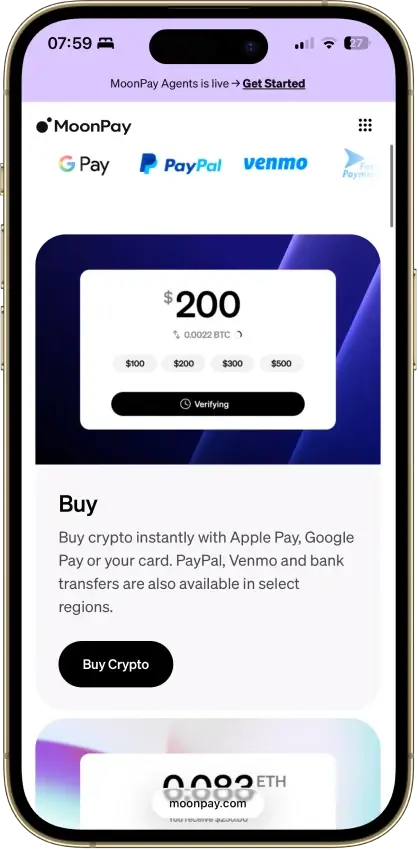
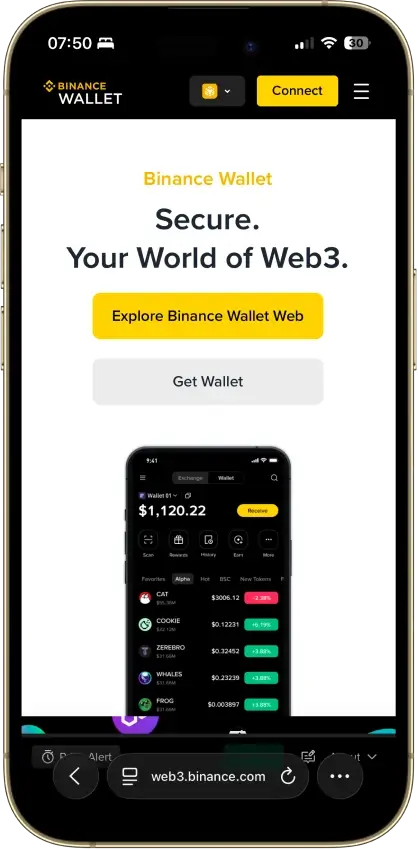
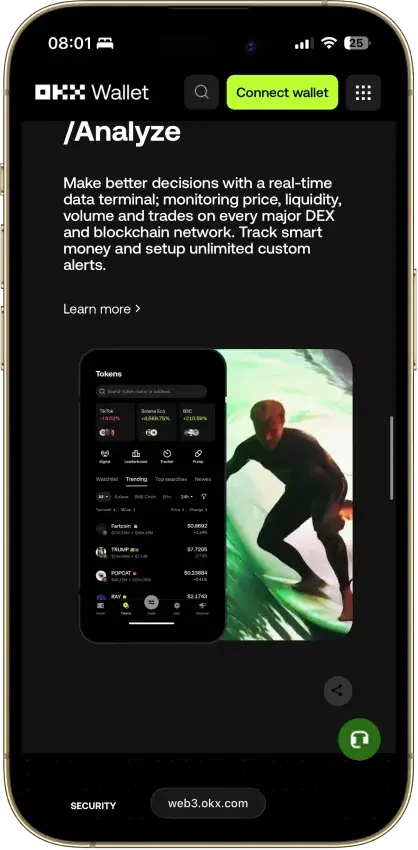
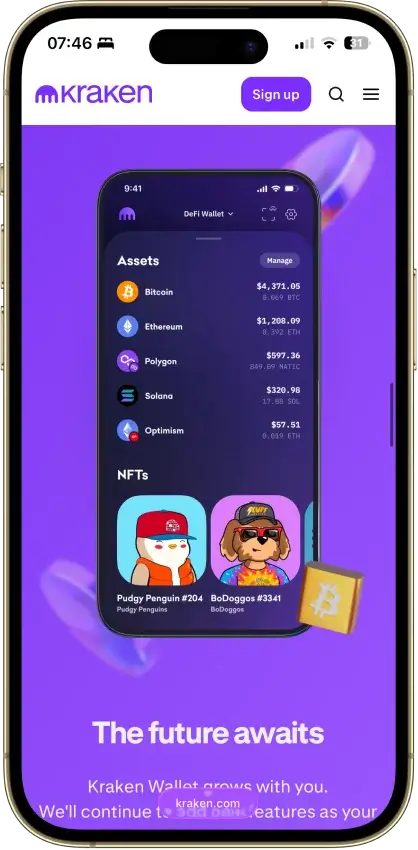
A hot wallet is a non-custodial wallet that runs on an internet-connected device (phone or browser). It’s the most practical choice for trading, DeFi, NFTs, and everyday transfers because it can connect to dApps quickly.
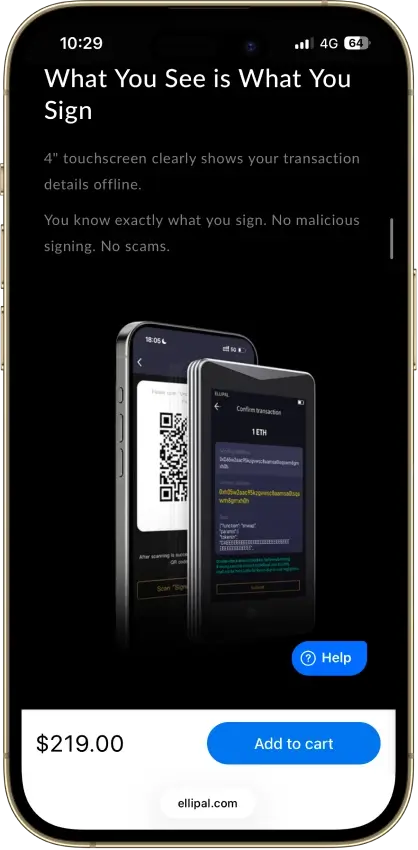
The main downside is exposure. Hot wallets are more vulnerable to phishing, malicious approvals, and fake websites. If you use DeFi, always read what you’re signing and review token approvals regularly.
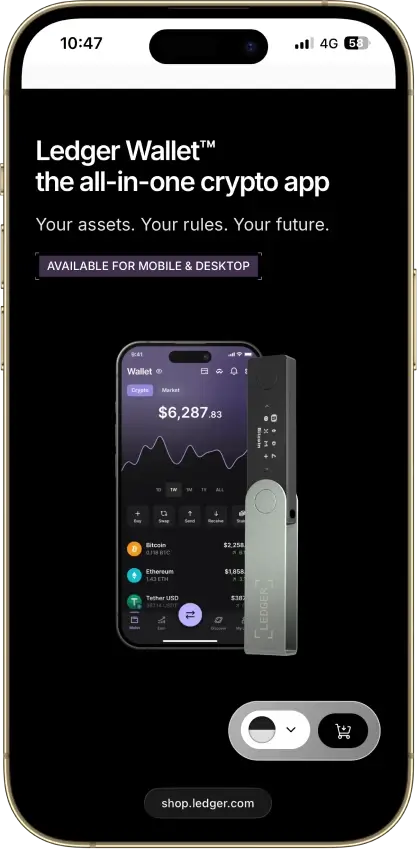
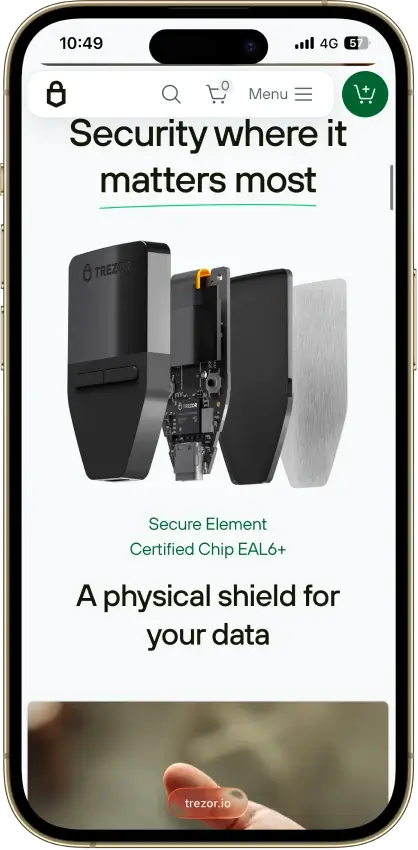
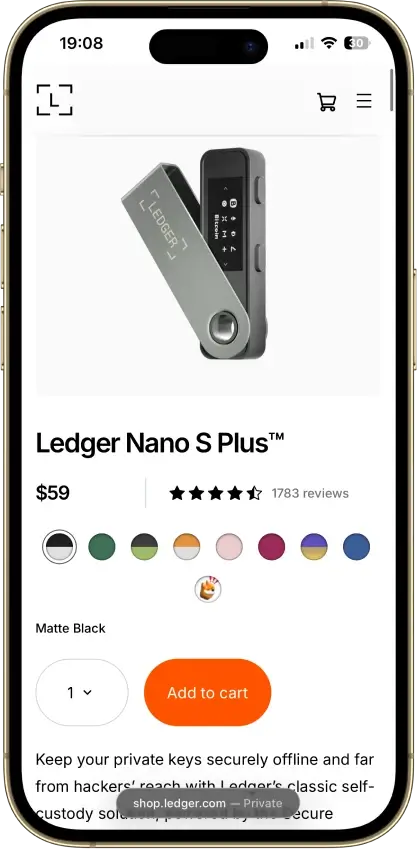
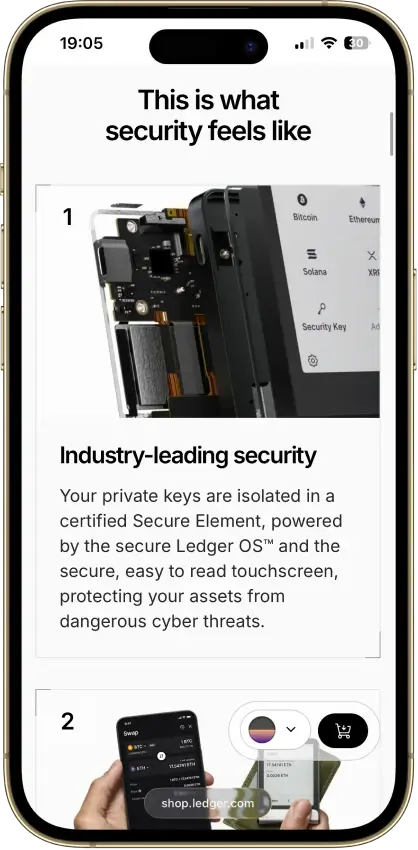
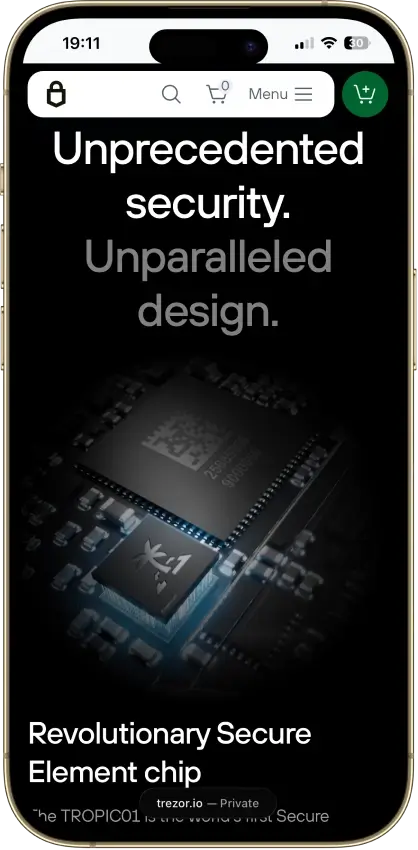
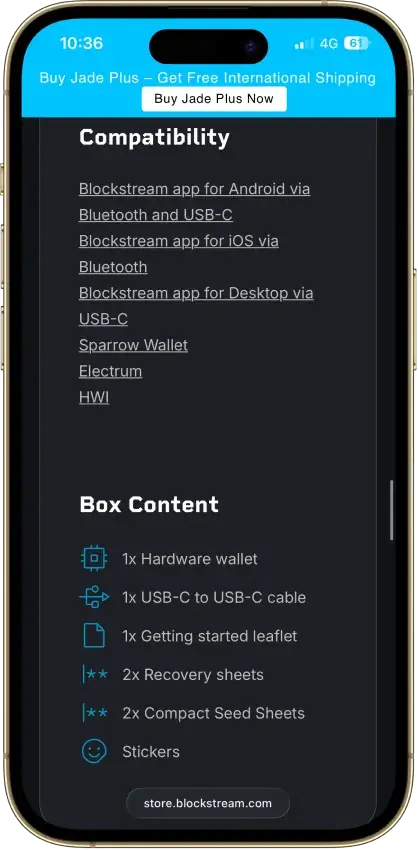
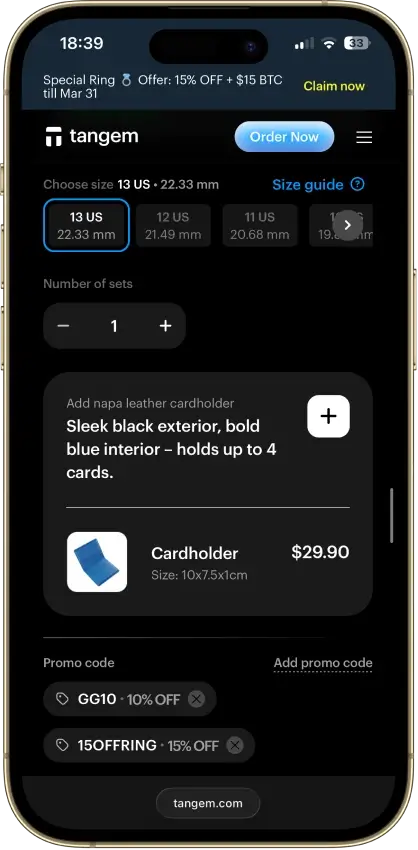
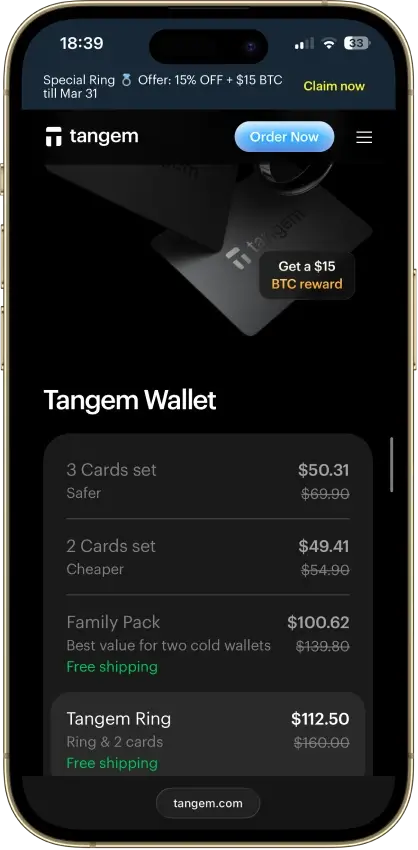
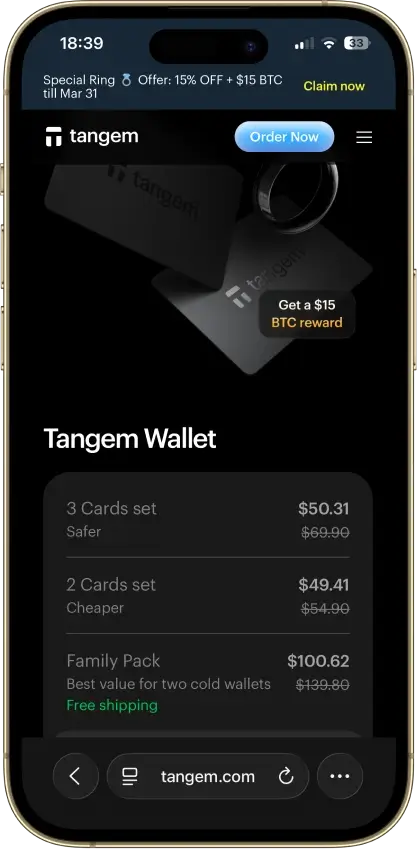
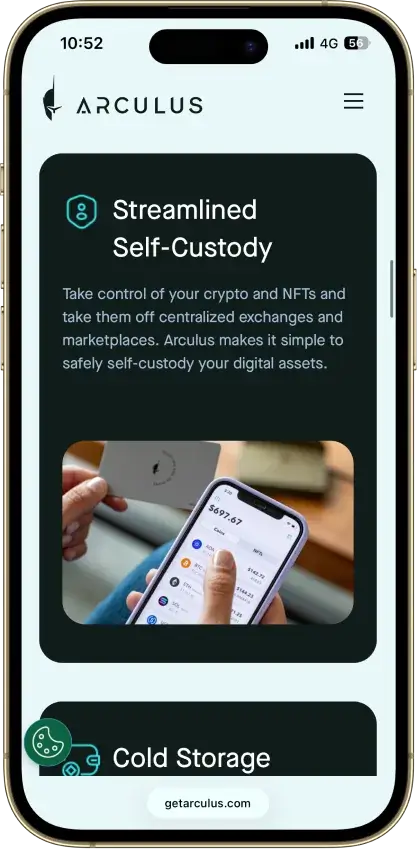
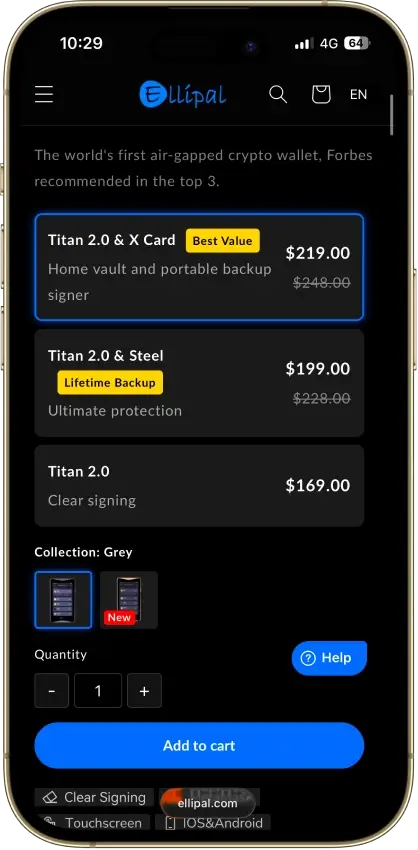
Cold Wallets
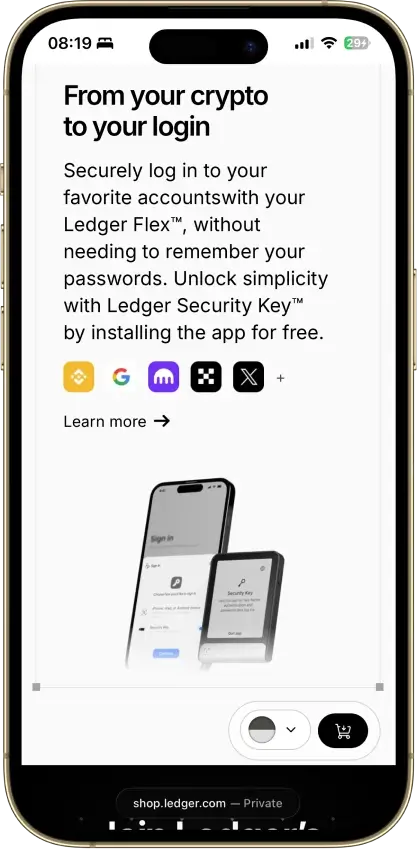
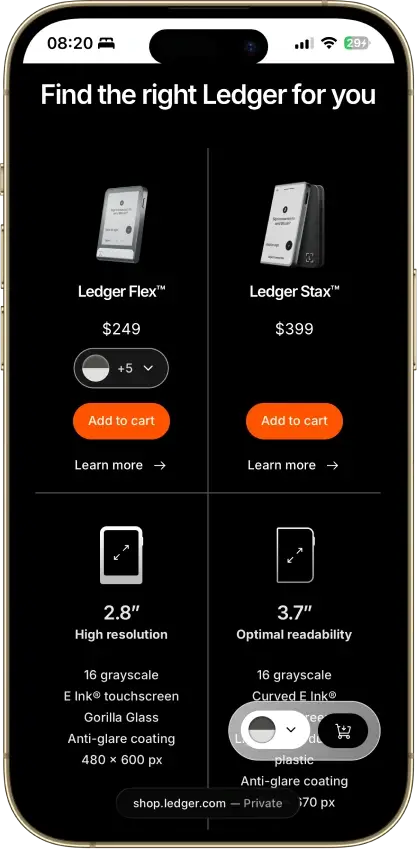
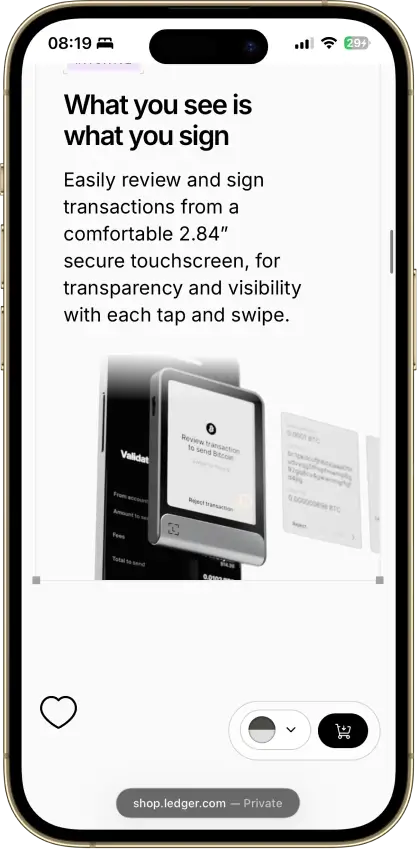
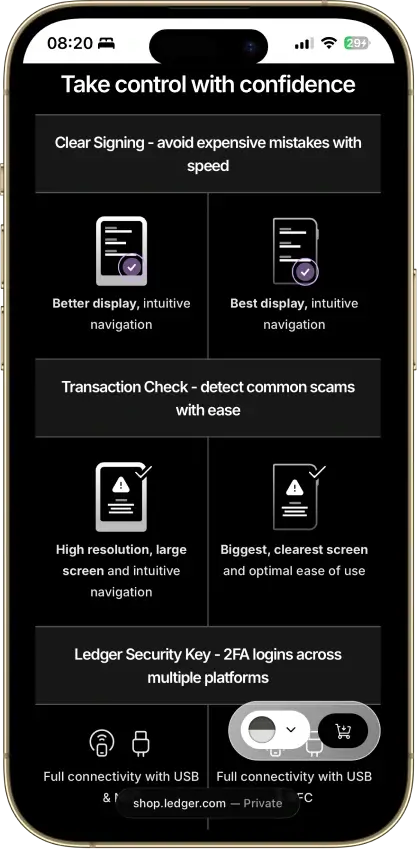
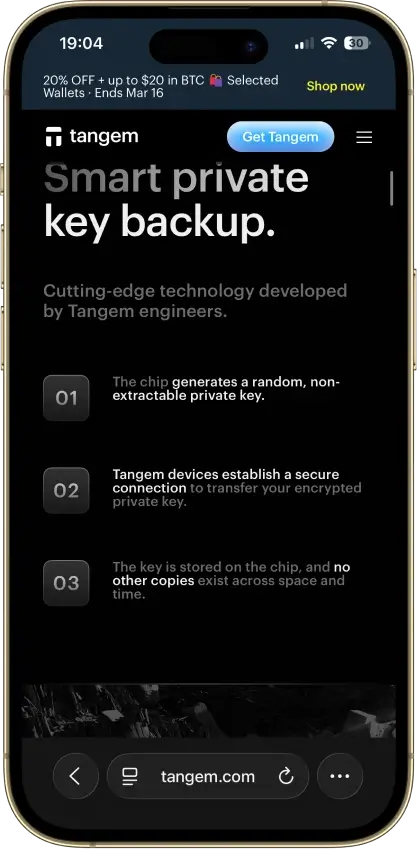
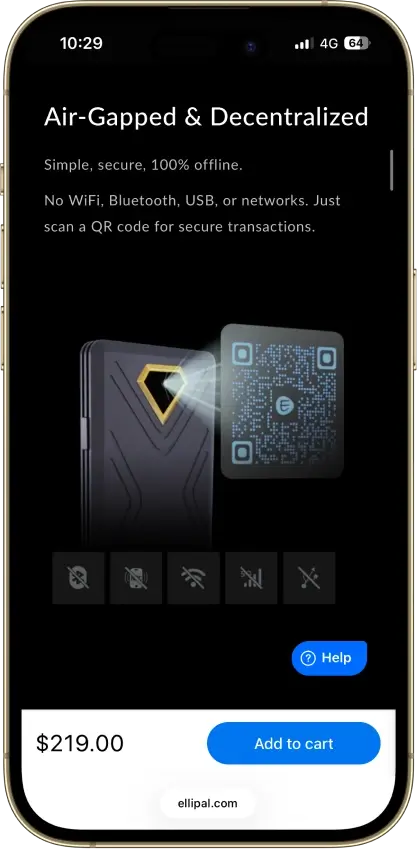
A cold wallet keeps your private keys offline, usually in a dedicated hardware device. In a self-custody setup, that’s a decentralized cold wallet (a non-custodial cold wallet). It’s the safer default for long-term holdings because your keys never live on an always-online phone or computer.
Offline signing, in one line: the hardware wallet signs the transaction on the device, and your phone or computer only broadcasts the signed transaction to the network.
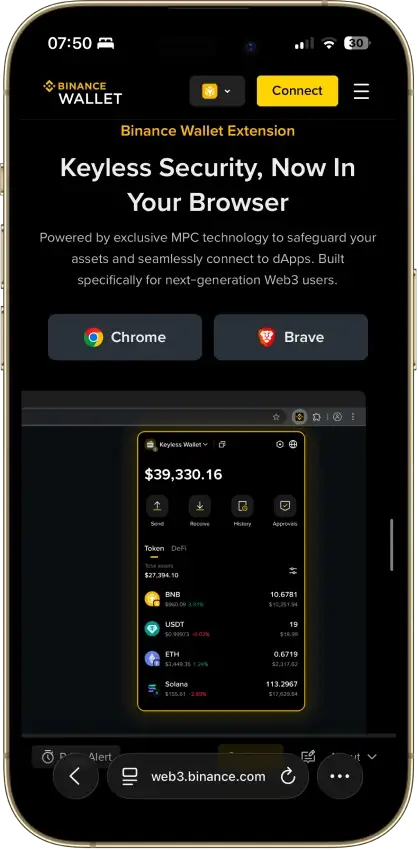
Browser Extension Wallets
Browser-extension wallets are popular for desktop DeFi because they integrate directly with Web3 sites. They’re fast and convenient, especially for EVM apps, but they also make it easier to sign the wrong thing if you’re not careful.
Browser support is not always interchangeable. For example, Phantom officially supports Chrome for full extension support; other Chromium browsers may work, but they are not fully supported the same way.
Keep your habits tight: bookmark key dApps, double-check URLs, and don’t approve unlimited spending unless you understand why you need it.
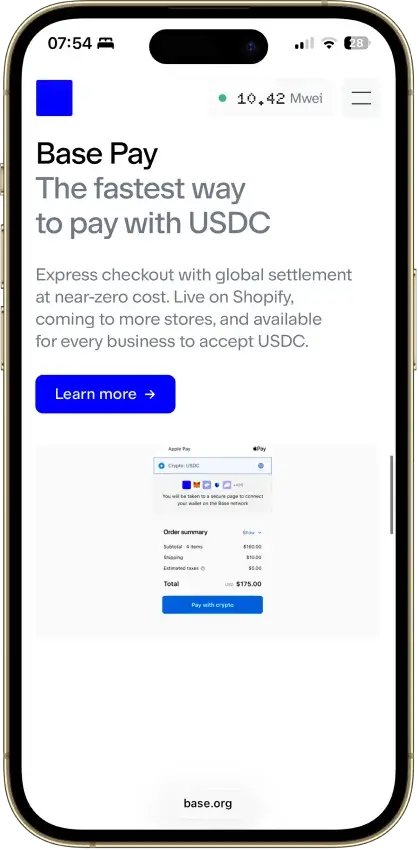
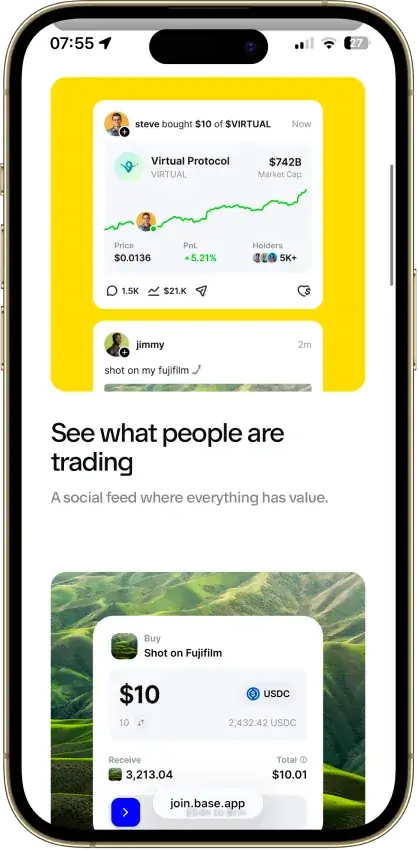
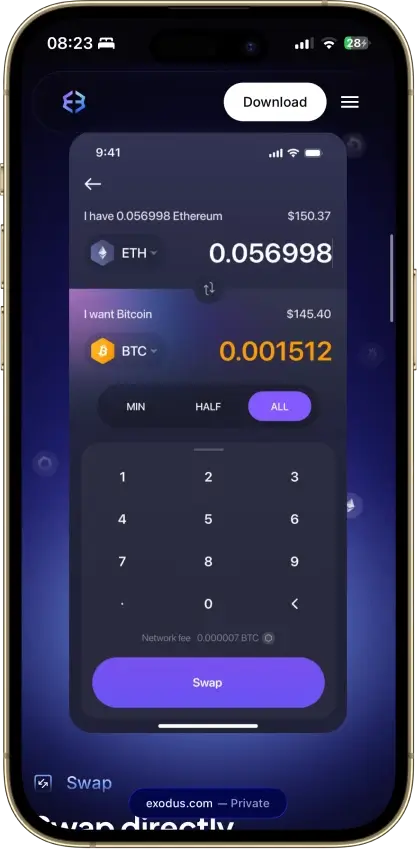
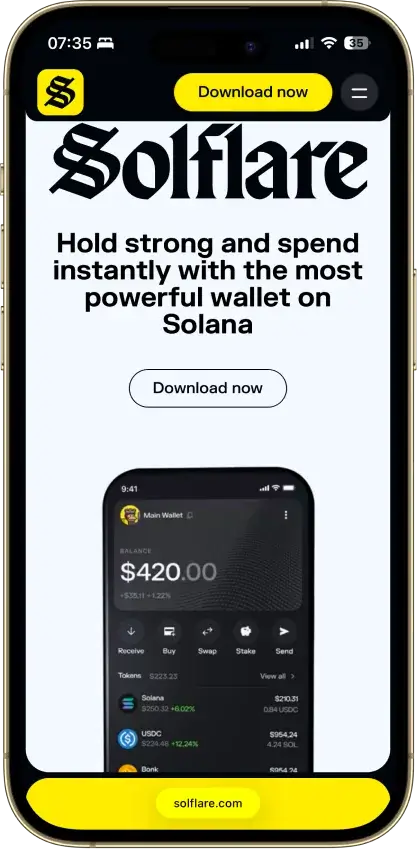
Mobile Wallet Apps
A decentralized wallet app on mobile is great for everyday use because it’s always with you. It can also connect to dApps through an in-app browser or WalletConnect.
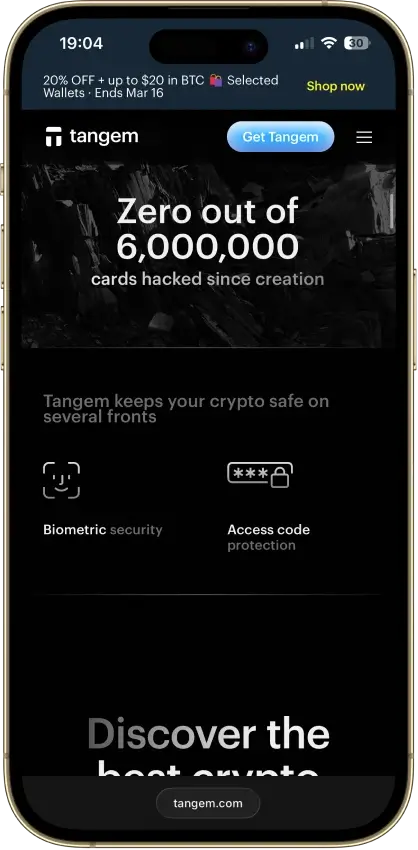
Mobile dApp access also differs by wallet. Phantom mobile connects only inside Phantom’s in-app browser, while Tangem relies on WalletConnect rather than a built-in browser.
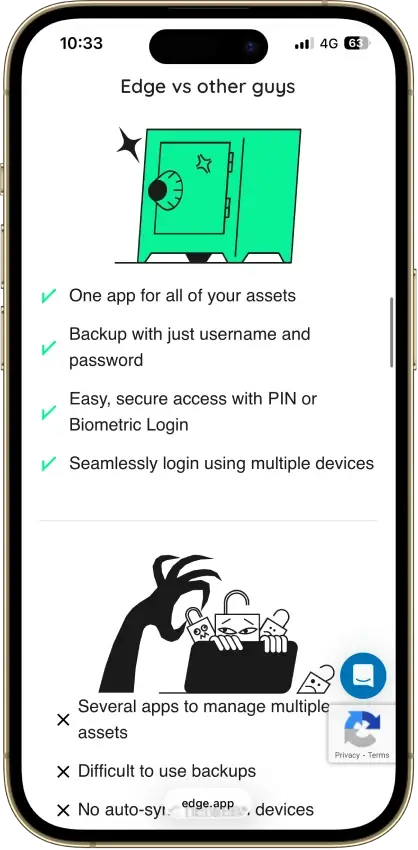
Basic setup matters here. Use a strong device lock, enable biometric or PIN protection inside the wallet, and make sure you have a verified backup of your recovery method before you move meaningful funds.
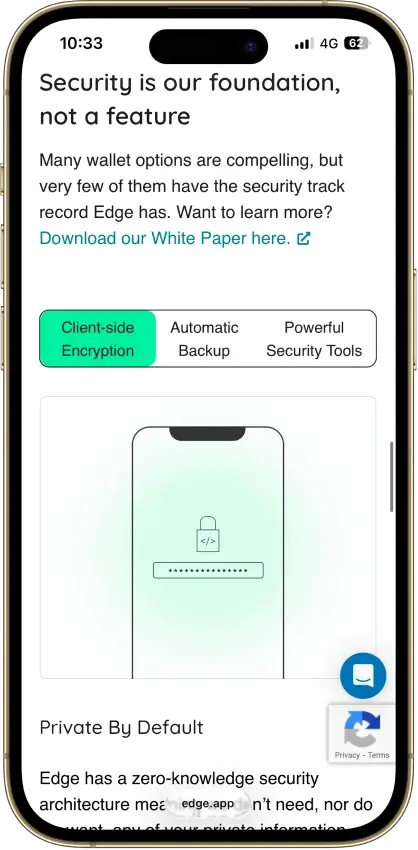
Seed Phrase Vs Seedless / MPC Recovery
Most self-custody wallets use a seed phrase (recovery phrase). It’s simple and portable, but it’s also a single point of failure. If someone gets your seed phrase, they can take your funds.
“Seedless” recovery often uses passkeys, secure enclaves, or MPC-style recovery, where access is restored through multiple approvals or shares. This can reduce the risk of a single phrase being stolen, but it also means your recovery depends on the wallet’s process and any third-party components involved. The best choice is the one you can back up correctly and keep secure.
What Happens To Your Crypto Wallet If You Lose Your Phone?
If your wallet uses a seed phrase, recovery depends on that phrase. If it uses an email or seedless flow, recovery depends on that wallet’s specific process.
Phantom can be restored with Google or Apple plus a four-digit PIN (depending on the method you used while signing up for the account), Trust Wallet offers optional encrypted cloud backup, Trezor supports Multi-share Backup, and Ledger Flex includes Ledger Recovery Key alongside standard recovery-phrase restore options.
The right model is the one you understand and can verify before you move real money into the wallet.
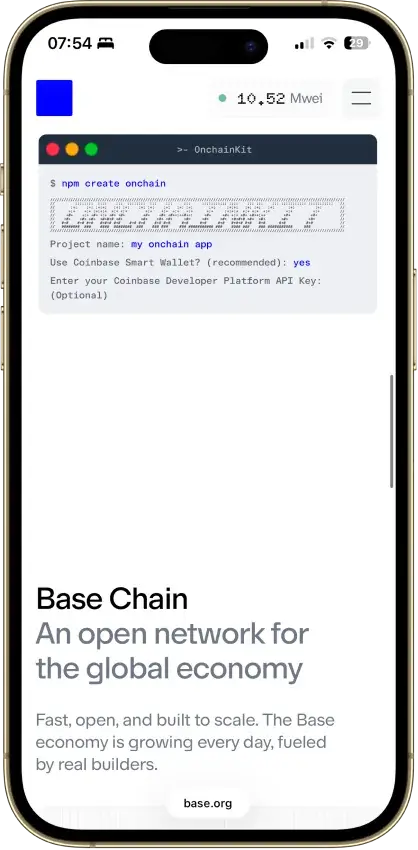
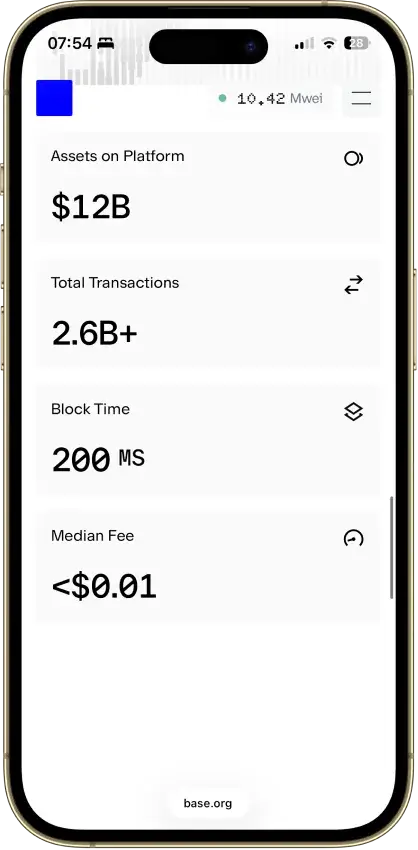
Smart Accounts And Account Abstraction
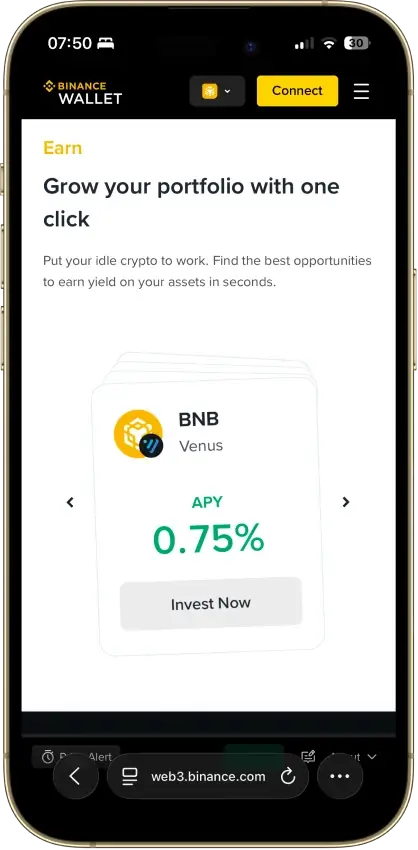
Some wallets now add smart-account features on top of self-custody.
In practice, that can mean batched actions, more flexible gas handling, or easier recovery flows. These features can improve usability, but they do not change the core question of who controls the keys and how recovery works.
Treat smart-account UX as a bonus layer, not a replacement for clear custody and backup design.
Decentralized Wallet Vs Cold Wallet
These terms aren’t the same. Decentralized / non-custodial describes who controls the keys. Cold describes whether keys are kept offline. You can have a decentralized hot wallet (self-custody on your phone), or a decentralized cold wallet (self-custody on hardware). The key question is always the same: do you control the private keys and the recovery method?
 Part 1 Advanced The Market Maker’s Exchange Checklist (Liquidity, Latency, and Risk Controls) Market makers and HFT desks: evaluate exchanges on execution quality, liquidity, latency, fees, margin, and security — with a WhiteBIT walkthrough. Open guide
Part 1 Advanced The Market Maker’s Exchange Checklist (Liquidity, Latency, and Risk Controls) Market makers and HFT desks: evaluate exchanges on execution quality, liquidity, latency, fees, margin, and security — with a WhiteBIT walkthrough. Open guide